This is an original article from the NIST Manufacturing Innovation Blog.
This blog is the second in a series on cybersecurity and Industry 4.0.
In blog one of this series on “Cybersecurity and Industry 4.0 – What You Need to Know” we discussed the four aspects of Industry 4.0: cyber-physical systems (CPS)/cobots, Internet of Things (IoT), cloud manufacturing and automation, as well as how they are interconnected. Strong cybersecurity practices protect those interconnections, ensuring manufacturers’ systems consistently deliver accurate data in a timely manner – something critical to the success of an Industry 4.0 model.
In the past, enterprise systems in manufacturing facilities had distinct boundaries. The shop floor was separated from the office functions of the company both physically and electronically. Few production systems were connected to each other or the internet. In some ways, this approach, commonly known as “air gapping,” gave reasonable protection for small manufacturers. Without the risks associated with connectivity, manufacturers were seen by attackers as hard targets and not worth the effort.
Today, with the growing use of the internet and mobile devices, boundaries between traditional information technology (IT) systems, production systems, operational technologies (OT), or other equipment have almost disappeared. With the recent increase in the number of employees working remotely, the boundaries that remained in place were weakened further. Meanwhile, attacks to get around the air gap have become well known. Manufacturing is now the most targeted industry for cybersecurity attacks.
The fundamental guiding principle of cybersecurity is the CIA triad – confidentiality, integrity and availability. Confidentiality limits access to sensitive company information, integrity ensures that company data and equipment remains trustworthy and accurate, and availability provides timely access to company data and equipment. Other attributes are sometimes added to the CIA triad, such as privacy and safety, but these are the generally accepted core principles and are things any Industry 4.0 adopter should consider.

The CIA triad is a model used to represent three core principles of cybersecurity: confidentiality, integrity and availability.
What Manufacturers Need to Consider With Industry 4.0 Implementation
My last blog introduced AthCo, a fictional medium-sized manufacturer of athletic apparel. AthCo had recently achieved rapid growth after the launch of its new athleisure collection, which relies on the inhouse development of a new breathable fabric. The production method for the fabric is company proprietary information and needs to be protected.
For many years, AthCo has used an Enterprise Resource Planning (ERP) system and a Customer Relationship Management (CRM) system. A great deal of data is produced from the ERP, CRM and the “back office,” including transactional information.
With the implementation of Industry 4.0 through the use of sensors, cobots, cloud-based data analytics, a programmable logic controller (PLC), and data visualization, AthCo leadership can now retrieve and access data from every stage of the production process. This provides an instant snapshot of production status and helps to monitor fluctuations and quickly address potential issues. Plus, the data AthCo now collects allows it to rapidly communicate internally and with its customers, suppliers and business partners about things such as inventory levels.
But AthCo is learning that these improvements are not without risks. AthCo, just like any manufacturing company, needs to build the right infrastructure that can support and protect the collection, transformation, storage and analysis of data.
Threats to Manufacturers
Manufacturing systems need to be protected against many types of threats. Most threats affecting small and medium-sized manufacturers fall into three categories:
- Traditional IT –These are the types of threat most companies are familiar with: ransomware, data loss or theft, and intellectual property theft. They often target a company’s IT infrastructure and employees through phishing attacks (i.e., fake emails) or weak passwords. Successful traditional attacks can cost a manufacturer time and money and damage its reputation and the manufacturer’s business partners and supply chain. Often, smaller manufacturers are vulnerable to these traditional attacks because they do not consistently monitor and update their cybersecurity protections.
- Operational Technology (OT) – Industrial control systems (ICS), industrial IoT (IIoT) or other shop-floor equipment usually have very little internal cybersecurity protection as they were always considered secure if air-gapped. Today, this equipment is often connected to the company network and internet, and attackers can compromise them even if they aren’t connected. Successful attacks to the OT environment can endanger proprietary company information, interrupt the manufacturing process, or impact the quality of products.
- Customized Software – Manufacturers frequently use software that has been adjusted, modified or adapted to fit the demands and requirements of their businesses. Often, software must be tailored to allow for communications among different manufacturing systems. These adjustments may unintentionally introduce security vulnerabilities. Additionally, to prevent the equipment from malfunctioning, the software isn’t updated or patched to address newly discovered vulnerabilities. If the custom software was not designed from the beginning with security as a priority, or if it’s not implemented and maintained correctly, it can be a point of entry used to gain access to other systems.
Let’s look at some scenarios that AthCo might face based on each of the three types of threats:
- Traditional IT – AthCo’s IT staff has been very involved in the implementation of Industry 4.0. In fact, it has been so busy that it overlooked a new software update that included a number of security updates. This allows a hacker to penetrate the company’s IT systems and gain access to its customer database. Although payments are processed using a third-party that wasn’t affected, customer names, addresses and order information were compromised. AthCo has to follow local data breach notification laws, which cost it several thousand dollars. Unfortunately, AthCo is unable to tell what other information or systems the hacker may have compromised, and its ability to trust its data and IT infrastructure is now fractured.
- Operational Technology (OT) – A disgruntled AthCo design department employee shoulder surfs the production manager’s remote access control credentials during an off-site meeting. Several days later, the employee uses the stolen credentials to remotely log onto the production system, bring up screens, and randomly click on things, hoping to do as much damage as possible. These actions result in a complete production shut down for three days as the manufacturer is forced to reconfigure its machines.
- Customized Software – AthCo has several pieces of older production equipment that still work but need custom software to connect the machines to the new production management systems. A local software developer customized some open-source software to provide this connection. Unfortunately, AthCo did not stress cybersecurity as a priority to the software developer and the software contained many vulnerabilities that were not managed. As a result, AthCo’s production methods for its new breathable fabric, the reason behind the success of its new collection, was stolen by its competitor through the vulnerabilities introduced in its custom software.
AthCo knows cybersecurity needs to be part of the company culture, especially as it moves toward increased Industry 4.0 implementation. Here are some things that you and AthCo can do to protect your investment:
- Have a cybersecurity awareness and training program for new and current employees that teaches what behaviors are appropriate, how to identify suspicious activity, and how to react if they see a problem. See this list of free and low cost online cybersecurity learning content compiled by NIST.
- Perform a cybersecurity risk assessment every year. This provides an understanding of which cybersecurity risks to focus resources on and prevents waste. See NISTIR 7621 Rev. 1, Small Business Information Security: The Fundamentals for a very simple guide on conducting a risk assessment.
- Have a conversation about cybersecurity with any service providers. Make sure that cloud service providers protect your data from misuse and disclosure, that cleaning or maintenance providers are trustworthy, and that critical utilities such as power or internet guarantee an appropriate level of “uptime.”
- Understand the cybersecurity practices of suppliers. AthCo could request that each supplier submit a completed Vendor Assessment Questionnaire. See NIST’s Assessment & Auditing Resources page. This will provide an understanding of the level of cybersecurity expertise within the supplier’s company.
AthCo will need to determine the level of risk it is willing to accept and what specific cybersecurity practices it will want to apply. A useful roadmap for reducing cybersecurity risk in manufacturing can be found at NISTIR 8133 Rev 1 Cybersecurity Framework 1.1 Manufacturing Profile.
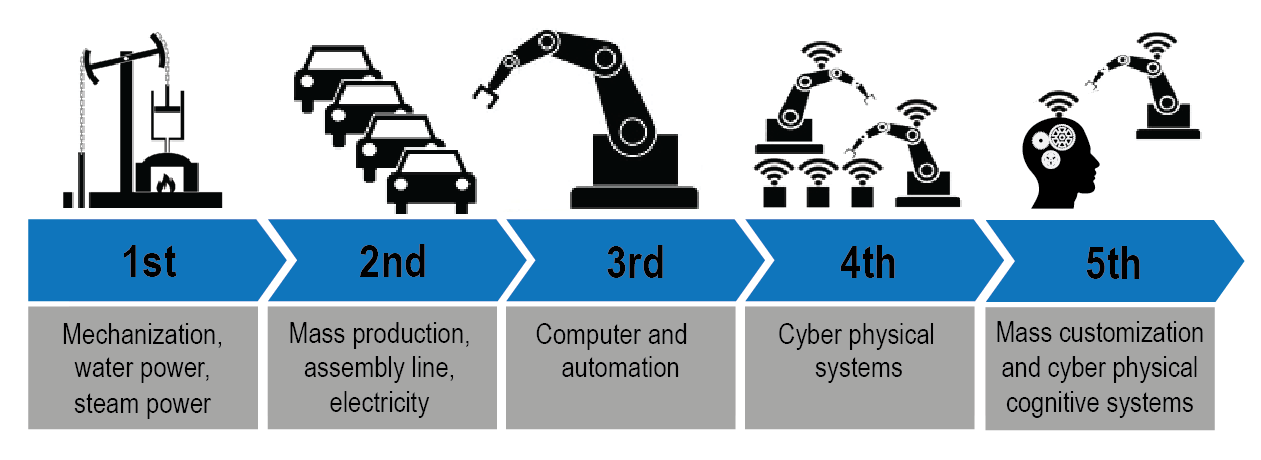
As Industry 4.0 matures and as we approach the fifth industrial revolution (5IR), your manufacturing company should expect to see the interconnection of data and technology as a competitive advantage over less technologically advanced companies. Cybersecurity will continue to be a critical component of successful implementation of Industry 4.0 and beyond.
For more information on cybersecurity and Industry 4.0, please contact IMEC.



